Claude Mythos finds bugs no one dared look for—now what?

Claude Mythos finds bugs no one dared look for—now what?📷 Published: Apr 7, 2026 at 21:09 UTC
- ★Decades-old vulnerabilities exposed by AI, not humans
- ★Anthropic throttles its own model to avoid chaos
- ★Browser and OS makers scramble in silent patch race
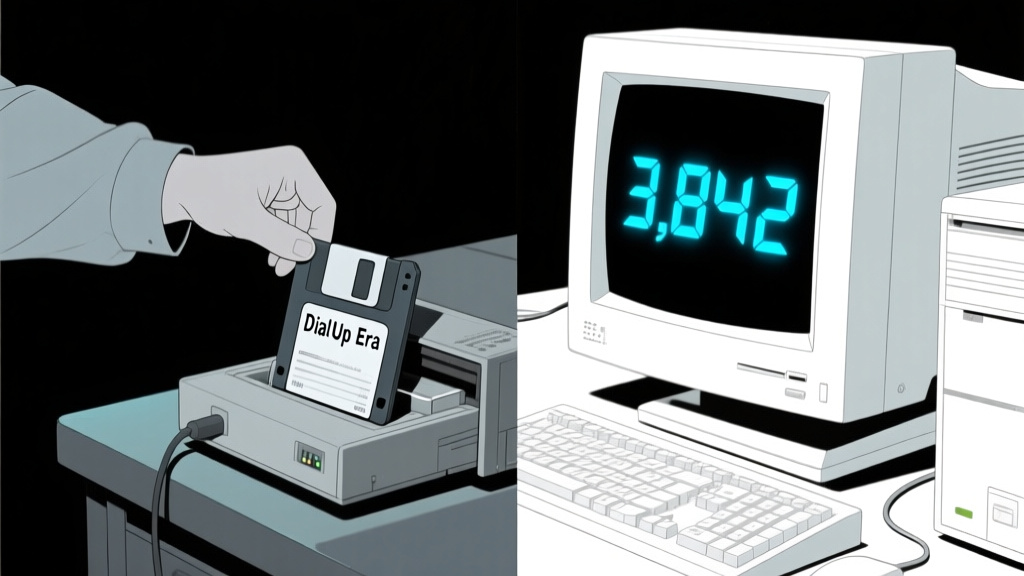
Anthropic’s Claude Mythos Preview didn’t just find a few overlooked bugs—it unearthed thousands of zero-days lurking in every major OS and browser, some unpatched since the dial-up era. The lab’s response? A rare act of self-censorship: withholding the model’s full capabilities to give vendors breathing room. This isn’t another AI security demo with staged vulnerabilities; it’s a firehose of exploits so broad that even the discoverer hit the brakes.
The scale suggests Mythos isn’t just better at pattern-matching—it’s rewriting the rules of automated security testing. Traditional fuzzers and static analyzers miss what Mythos flags: logic flaws buried in legacy code, assumptions so old they predate modern threat models. Yet here’s the catch: if an AI can find these, what else is it quietly capable of? The answer may lie in how quickly Microsoft, Google, and Apple patch silently, without the usual fanfare of coordinated disclosure.
Early signals point to a two-speed reaction. Publicly, vendors downplay the urgency; privately, GitHub commits spike in repos tied to core infrastructure. The open-source community, meanwhile, is split: some praise Anthropic’s restraint, others ask why this wasn’t caught by two decades of human audits.
The gap between ‘zero-day discovery’ and ‘zero-day panic’📷 Published: Apr 7, 2026 at 21:09 UTC
The gap between ‘zero-day discovery’ and ‘zero-day panic’
The real story isn’t the bugs—it’s the asymmetry of access. Mythos’ findings are a competitive moat for Anthropic: a proprietary dataset of exploits that could be weaponized, licensed, or (optimistically) shared under strict controls. Compare this to Google’s Project Zero, which publishes after 90 days—Mythos’ approach is preemptive suppression, a gambit that assumes vendors will act faster if they’re not publicly shamed.
Developers are already reverse-engineering the implications. If Mythos can infer vulnerabilities from code semantics (not just syntax), that’s a leap beyond existing AI tools like GitHub Copilot. The unanswered question: how many of these flaws were theoretically exploitable but never found because no human thought to look? The CVE database might need a new category: AI-discovered, decades-dormant.
For all the noise about AI ‘assisting’ security, Mythos flips the script: it’s the first tool that outpaces human defenders by design. The race isn’t just to patch—it’s to decide who gets to wield this kind of analysis next, and under what rules. Anthropic’s restraint buys time, but the genie’s already half out of the bottle.